NOTORIOUS HACKERS
Added on: 3rd Mar 2015
JEANSON JAMES ANCHETA
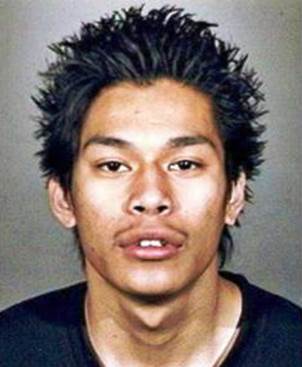
A dropout of Downey High School in California,
Jeanson James Ancheta became a hacker in 2004 after he
started to work with software robots called “botnets.”
His hacking practice began when he discovered rxbot,
a computer worm that has the capacity to infect and destroy
computer networks. He became the first person to have ever
been charged for controlling a huge number of hijacked
computers in the United States.
KEVIN POULSEN

A news editor at Wired.com, Kevin Lee Poulsen is a former
hacker whose most remarkable hack was when he took over the
telephone lines of the entire Los Angeles-based radio station
KIIS-FM as he intended to make sure that he would be the
102nd caller in order to win a Porsche 944 S2.
After he was released from prison, he decided to leave the
computer programming world and become a journalist to
distance himself from his criminal past.
ALBERT GONZALEZ
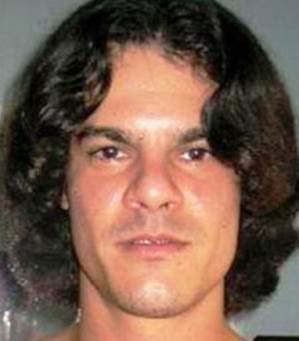
A computer criminal best known for having masterminded
and orchestrated a string of credit card thefts in the
United States that brought in 170 million US dollars to his
personal account, Albert Gonzalez is a computer hacker who
is said to have committed the biggest and most controversial
fraud in history. He used SQL injections in his operations to
steal computer data from private computer networks and launch
ARP spoofing attacks, a technique that sends fake messages
to local area networks.
GEORGE HOTZ
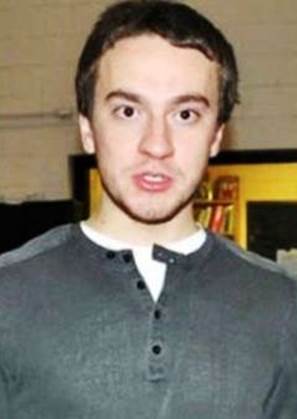
An alumnus of the John Hopkins Centre for Talented Youth program,
George Francis Hotz is known for unlocking the iPhone to allow
it to be used with other wireless carriers. He was also the one who
developed the limera1n jailbreak tool, the tool that could remove the
limitations of Apple devices such as iPad, iPhone, iPod touch, and
Apple TV. He was also sued by Sony for hacking the PlayStation3.
KEVIN MITNICK
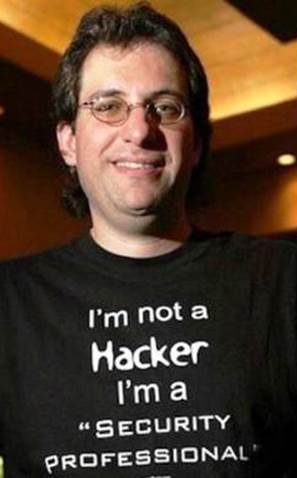
An American computer security consultant, Kevin David Mitnick
is one of the most notorious hackers of the 20th century.
He got involved in several computer and communications-related
crimes and even became one of the most wanted computer
criminals in the United States. At a very young age of 12,
Kevin Mitnick begun to use his social engineering skills to
circumvent the punch card system used in Los Angeles buses.
GARY MCKINNON

Convicted for having hacked a total of 97 US-based military
and NASA computer systems, Gary McKinnon is a systems
administrator based in Scotland. In 2002, he was known for having
perpetrated the largest military computer hack of all time after
shutting down a network of 2,000 computers in the US military and
deleting critical files such as weapons logs in just a matter of 24 hours.
This rendered the US military network inoperable for days.
ADRIAN LAMO

Adrian Lamo first caught the attention of the media after he
broke into several high-profile computer networks such as
The New York Times, Yahoo!, and Microsoft. He also became
known for operating Inside-AOL.com, an AOL watchdog website.
He has performed several authorized and unauthorized security
checks for high-profile networks and yet never asked for a fee.
Lamo was complimented for fortifying the corporate
security of Worldcom.
JONATHAN JAMES

A hacker who was imprisoned at a juvenile age for
violating the cybercrime law, Jonathan James was known for
committing several unauthorized intrusions in computer
networks and systems including those of Bellsouth and
the Miami-Dade School. In his early 20’s, he admitted to the
authorities that he had installed an illegal backdoor in a
computer server in Virginia to access the usernames and
passwords of some 300 internet users, particularly DRTA
employees and military men.
OWEN WALKER

A hacker based in New Zealand, Owen Walker was a ringleader
of a notorious international hacking organization that was
estimated to have caused about $27 million worth of damages to
several groups. He did not receive formal training in computer
programming since he dropped out of school because of bullying.
He masterminded the attack of the computer network of the
University of Pennsylvania through the use of unauthorized botnets
which he established himself.

Comment on this